I have an early post of OWASP top 10 2021: OWASP. That post compares the top 10s from 2013 to 2021 (in draft). Many people might be curious on how log4j vulnerabilities are mapped with OWASP top 10. Here’s my one page press picture:
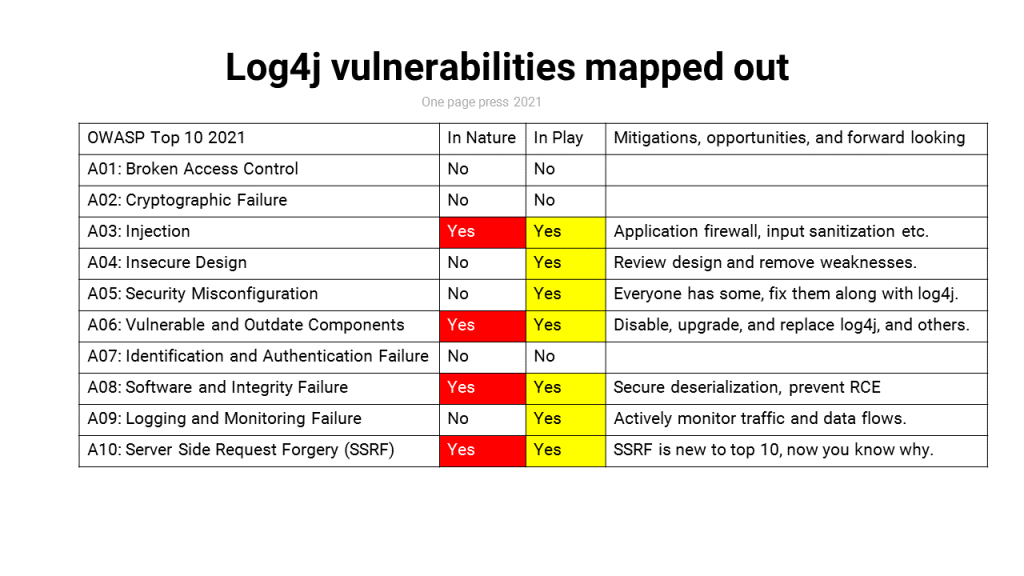
The image speaks for all and replaced 11 paragraphs of words.
The most scary part of log4j problem is, hinted with my picture, it does not require breaking into your computer systems with credentials stealing or access control breach. Once succeeded, I run my code on your network. The easy and destructive part is more worrisome than the sophistication part.
I list a couple of references if you like to know more about OWASP and log4j.
- OWASP top 10 reference: https://owasp.org/Top10/
- Log4j CVE details: https://www.cvedetails.com/vulnerability-list/vendor_id-45/product_id-37215/Apache-Log4j.html
My last post log4j vulnerability what and how in plain language mentioned fixes and recommendations. I hope you and your organization take log4j seriously and act with your plan. You are also racing with time.